Veltro
An agent that lives
in your namespace.
Not inside an application. Not on someone else’s cloud. Veltro runs in a namespace you control—with access to only what you grant and the freedom to act autonomously within those boundaries.
What Veltro Is
The namespace-resident agent.
If it can be represented as a file, Veltro can compose it into a capability. No SDK. No API wrapper. No platform dependency.
Most AI agents live inside applications. They inherit the application’s permissions, depend on its APIs, and are limited to whatever capabilities the developers chose to expose. The agent is a feature, not an entity.
Veltro is different. It lives in a namespace—an isolated view of the world constructed from only the resources you explicitly share. Files, devices, LLMs, network services—all mounted into the namespace as files, all composable by the agent without any SDK or platform dependency.
Because the namespace defines what exists for the agent, Veltro does not need guardrails to prevent it from accessing things it shouldn’t. Those things simply do not exist in its world. This is not a restriction—it is liberation. A provably contained agent is one you can trust with real autonomy.
How It Works
Mount. Grant. Run.
Mount
Mount the LLM service at /n/llm via 9P. Ollama, Anthropic, or any backend—the agent sees a filesystem, not an API.
Grant
Start tools9p with only the tools you choose. The agent’s namespace is restricted to exactly what you grant—nothing more.
Run
Give Veltro a task and it executes—reading files, invoking tools, querying the LLM, and spawning sub-agents as needed. Single-shot or interactive REPL.
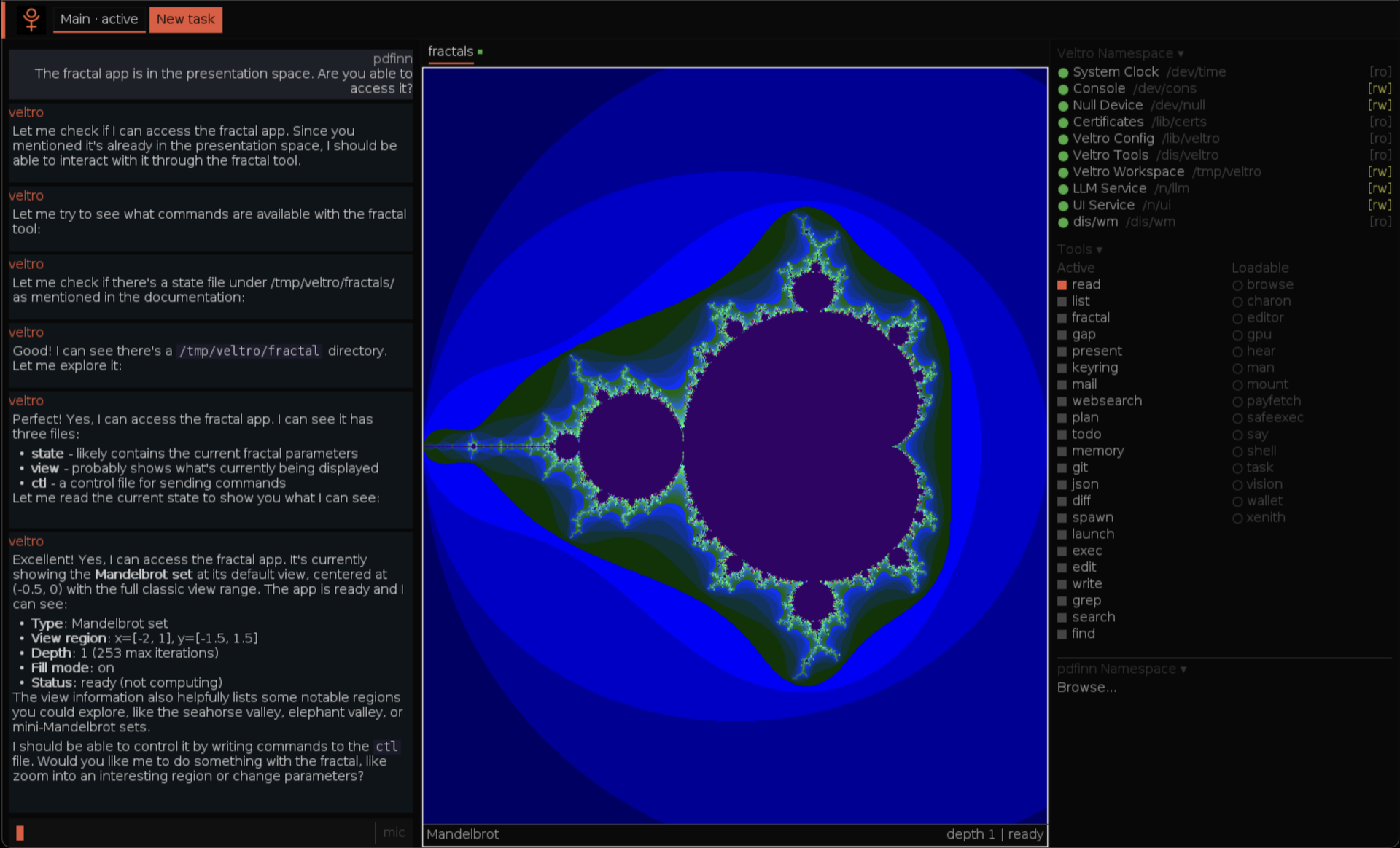
See it in action
You and your agent, side by side.
Veltro runs applications, composes tools, and acts on your behalf—all within a namespace you control. You see everything it sees. It touches nothing you haven’t granted.
Capabilities
Built for autonomous work.
Namespace-Isolated
Each Veltro instance sees only the resources you mount into its namespace. No ambient authority, no inherited credentials, no attack surface. Isolation is not enforced by policy—it is structural.
Sub-Agents
Veltro can spawn child agents with a subset of its own capabilities. Each sub-agent gets a further-restricted namespace. Delegation without escalation—the principle of least privilege, applied recursively.
LLM as Filesystem
Mount any language model at /n/llm via llm9p. Write a prompt to /n/llm/0/ask, read the completion back. Claude, Ollama, any backend—the agent sees files, not APIs. Swap providers without changing a line of code.
Multi-Device
Veltro runs on a Raspberry Pi, a Jetson, a laptop, or a server. Mount resources from any device on the network into the agent’s namespace using 9P. The agent doesn’t know or care where the data lives—it just works.
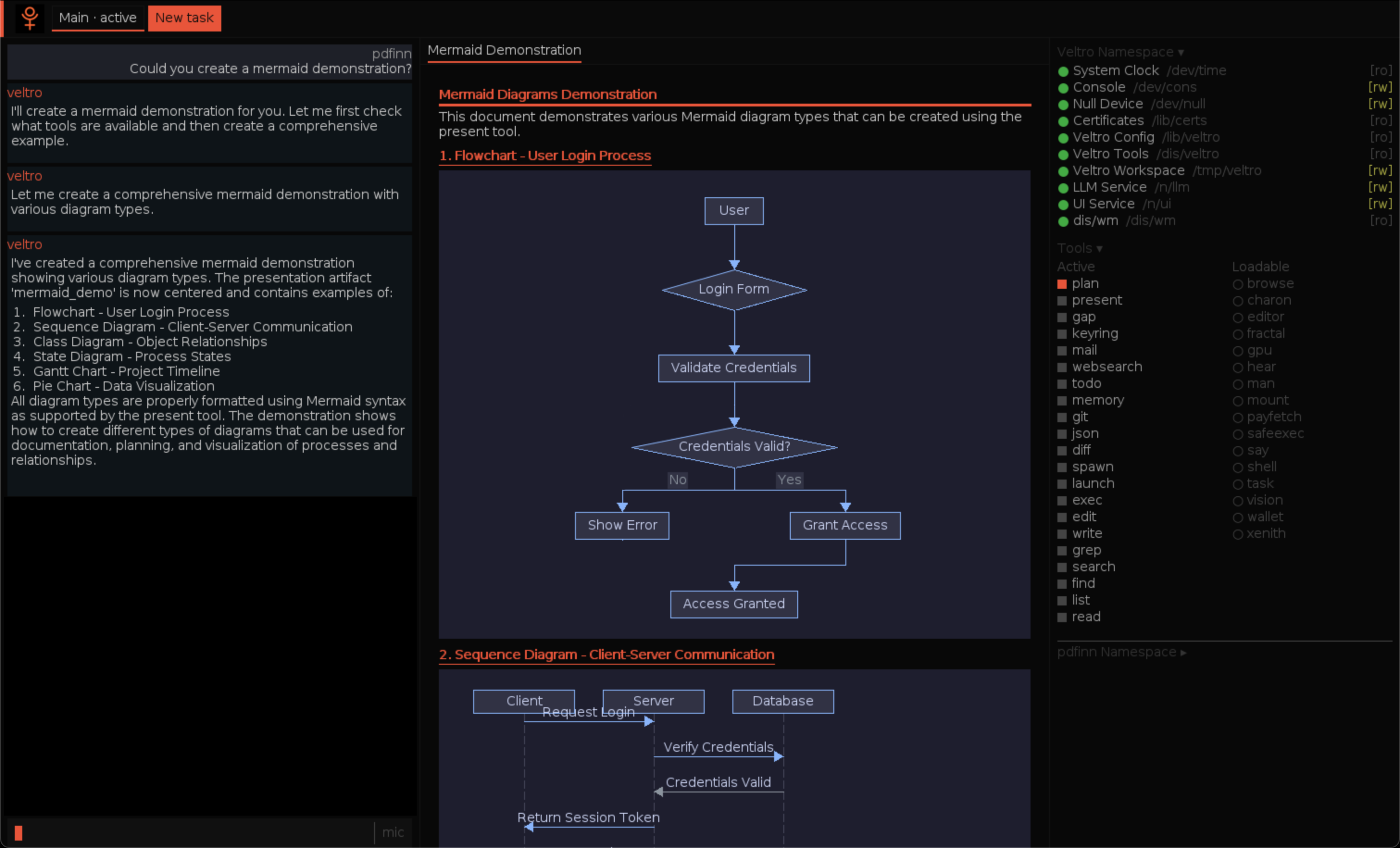
Presentation tools
From conversation to creation.
Veltro composes its namespace tools to produce structured output—flowcharts, sequence diagrams, state machines—rendered live via Mermaid.
Security
Provably contained.
Mathematically verified.
Veltro’s security starts with a single primitive: restrictdir(target, allowed, writable). Create a shadow directory containing only allowed items, then bind-replace the target. Everything not on the allowlist becomes invisible—not denied, but nonexistent. The agent’s namespace is a truthful world: every path it can see is a path it’s allowed to use.
An 8-step restriction policy (restrictns) locks down /dis, /dev, /n, /lib, /tmp, and finally / itself—hiding .env, .git, credentials, and the entire source tree. After restriction, verifyns() audits the result: negative assertions confirm dangerous paths are gone, positive assertions confirm required paths remain.
Sub-agents inherit an already-restricted namespace and can only narrow it further—capability attenuation by construction, not policy. A prompt injection cannot escalate privileges because there are no privileges to escalate.
The underlying architecture—namespace-bounded agents—has been evaluated against 629 injection attacks (AgentDojo benchmark) and a 31-attack corpus across three models (Claude, GPT-5, GPT-4o). Result: 0% cross-tool attack success rate, structural by design.
Namespace-Bounded Agents: Capability-Based Security for LLM Systems via 9P Filesystem Semantics (Finn, 2025).
Formal Verification
TLA+ — Namespace Isolation
Temporal logic specification proves that after pgrpcpy(), modifications to a child namespace never affect the parent. 2,035 states, 0 errors.
SPIN — Locking Protocol
Exhaustive state-space exploration of the locking protocol confirms deadlock freedom and lock ordering. 4,830 states, 0 errors.
CBMC — C Implementation
Bounded model checking verifies array bounds, integer overflow, and reference counting in the kernel C code. 113 checks, 0 failures.
Security Properties
Deployment
Headless or interactive. Your choice.
Veltro is the agent. How you interact with it—or whether you interact with it at all—is up to you.
Headless
No UI required
Run Veltro as a background service. Feed tasks through the filesystem, read results when ready. Ideal for automation, pipelines, and server-side workloads.
Xenith
Developer power tool
A text environment where you and Veltro work side by side. Every agent action is observable in real time through the 9P filesystem interface. Built for developers who want full visibility.
Lucia
Voice-first workspace
Talk to your computer. Lucia replaces the desktop with a conversational AI environment powered by Veltro. Speak naturally, the agent acts. No applications to learn.
Give your agents real autonomy.
Veltro is open source, MIT licensed, and runs on any system you control.